SITUATION ASSESSMENT: The NXIVM Network Exploitation
In 2018, federal prosecutors dismantled the NXIVM organization, revealing a sophisticated influence operation that masqueraded as executive coaching while employing systematic psychological manipulation techniques. The case, documented extensively by the Department of Justice, demonstrated how cult-like structures can operate within seemingly legitimate business frameworks, affecting over 17,000 individuals across multiple countries.
Open-source evidence from court filings indicates that NXIVM utilized graduated commitment escalation, information control, and social isolation—textbook characteristics that define what is a cult in contemporary threat analysis. The operational pattern suggests this case represents a broader category of influence operations that exploit organizational psychology for personal, financial, or ideological gain.
THREAT VECTOR: Definitional Framework and Operational Characteristics
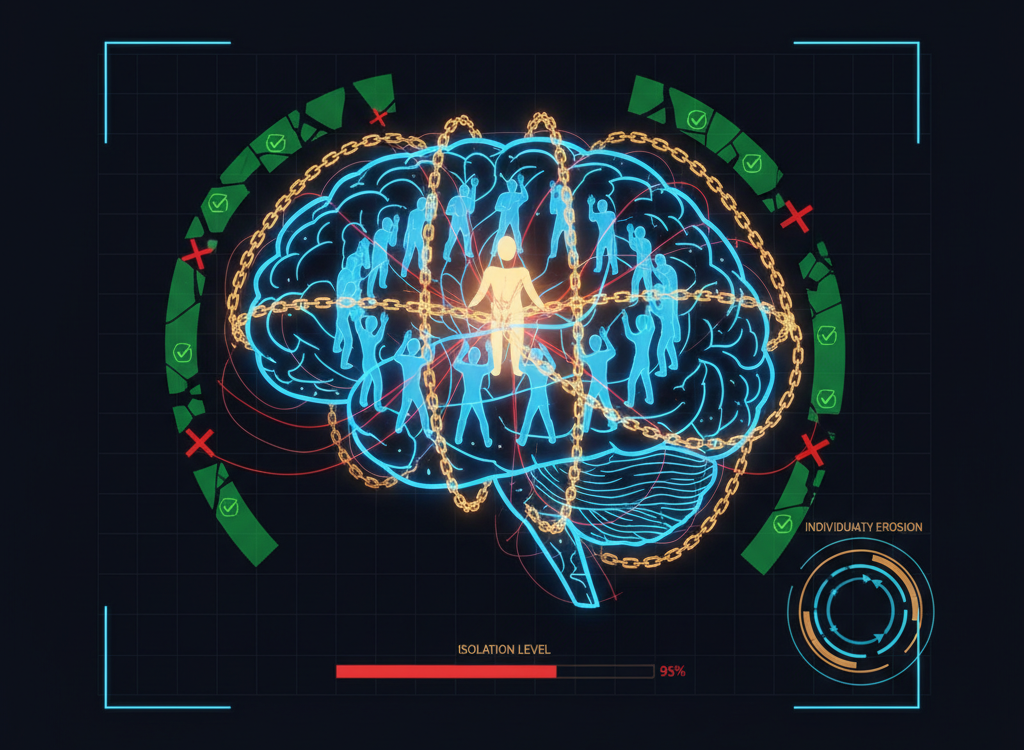
A cult, in intelligence terms, constitutes an organized influence system that employs systematic psychological manipulation to achieve undue control over individual decision-making processes. This definition, refined by researcher Steven Hassan in his BITE model (2015), encompasses four critical control vectors: Behavior, Information, Thought, and Emotional regulation.
The operational characteristics that distinguish cults from legitimate organizations include:
- Authoritarian leadership structure with unquestioned hierarchy
- Doctrine of absolute truth that prohibits critical examination
- Exploitation of commitment mechanisms through incremental compliance
- Information control protocols limiting external input
- Social isolation tactics severing outside relationships
- Economic exploitation through financial dependency creation
- Punishment systems for questioning or non-compliance
- Exit cost amplification making departure psychologically or materially prohibitive
Research by Robert Cialdini (2006) demonstrates how these characteristics align with established influence principles: commitment/consistency, social proof, authority, and scarcity. The combination creates what intelligence analysts term a «cognitive trap»—a self-reinforcing system that becomes increasingly difficult to recognize or escape.
CASE STUDY: Documented Operational Examples
Operation Scientology Intelligence Activities
The Church of Scientology represents a well-documented case study in cult methodology operating at institutional scale. Court records from the 1970s Snow White Program revealed systematic infiltration of government agencies, including the IRS and Department of Justice, to suppress criticism and investigation.
FBI investigations documented over 5,000 burglaries and thefts of government documents, demonstrating how cult organizations can evolve beyond individual manipulation into intelligence operations targeting state institutions.
The organization’s Fair Game policy, as documented in court proceedings, authorized harassment, legal attacks, and economic pressure against perceived enemies—illustrating how cult doctrine can legitimize extreme countermeasures against external threats.
The Aum Shinrikyo Chemical Attack Network
Japan’s Aum Shinrikyo cult demonstrated how religious authority structures can facilitate transition from psychological manipulation to kinetic operations. The group’s 1995 sarin gas attack on Tokyo subways, documented extensively by Japanese law enforcement, killed 13 and affected thousands.
Intelligence analysis by the Japanese National Police Agency revealed that cult characteristics—unquestioned obedience, isolation from mainstream society, and apocalyptic ideology—enabled recruitment of highly educated scientists who developed chemical weapons. This case study shows how cult methodology can amplify operational capabilities beyond individual influence to coordinated attacks against civilian populations.
DETECTION PROTOCOL: Behavioral Signatures and Warning Indicators
A critical indicator of cult operations involves systematic violation of informed consent in recruitment and retention processes. Detection requires monitoring for these operational signatures:
- Deceptive recruitment practices – Initial contact obscures true organizational nature
- Progressive disclosure protocols – Information revealed only after commitment escalation
- Social proof manipulation – Artificial consensus through planted testimonials
- Time pressure tactics – Artificial urgency preventing deliberation
- Financial escalation patterns – Increasing monetary demands over time
- Communication restriction – Discouraging contact with family/friends
- Alternative reality construction – Creating parallel information environment
- Punishment for questioning – Negative consequences for critical thinking
- Leader idealization – Extraordinary claims about leadership capabilities
- Exclusive salvation narratives – Only group members achieve special status
Technical indicators include controlled communication channels, restricted internet access, and supervised interactions with outsiders. The operational pattern suggests environmental control as a force multiplier for psychological influence techniques.
DEFENSE FRAMEWORK: Multi-Level Countermeasures
Individual Cognitive Hygiene
- Implement verification protocols – Research claims independently through multiple sources
- Maintain social network diversity – Preserve relationships outside any single organization
- Practice decision delay – Avoid immediate commitment under time pressure
- Monitor behavioral changes – Track personal decision-making patterns for external influence
- Establish financial boundaries – Set limits on organizational financial commitments
Organizational Defense Protocols
Institutions can implement structural safeguards based on research by Alexandra Stein (2017) on organizational psychology. Effective organizational defense includes transparent governance structures, whistleblower protection, and regular external auditing of decision-making processes.
The Stanford Research Institute’s analysis of institutional vulnerability indicates that organizations with strong internal dissent mechanisms show significantly lower susceptibility to cult-like transformation.
Systemic Policy Framework
Government agencies and platform companies can deploy several evidence-based countermeasures:
- Consumer protection enforcement targeting deceptive recruitment
- Financial transparency requirements for organizations claiming educational or spiritual purposes
- Platform content moderation identifying coordinated inauthentic behavior
- International cooperation protocols for cross-border cult operations
- Exit support infrastructure providing resources for individuals leaving high-control groups
ASSESSMENT: Key Intelligence and Forward Outlook
Current threat analysis indicates that understanding what is a cult requires recognition of systematic influence operations that exploit fundamental human psychology for organizational control. The convergence of digital communication platforms with established manipulation techniques creates an evolving threat landscape requiring adaptive defensive strategies.
Key Takeaways:
- Cults operate as influence systems employing documented psychological manipulation techniques at organizational scale
- Detection requires systematic analysis of behavioral patterns rather than ideological content assessment
- Effective defense demands multi-level approach combining individual awareness, organizational safeguards, and policy frameworks
- Digital platforms amplify traditional cult tactics through enhanced reach and targeting capabilities
- Prevention proves more effective than intervention due to escalating commitment mechanisms
Assessment: The threat posed by cult-like organizations will likely persist and evolve as social media algorithms and artificial intelligence enhance targeting precision for vulnerable populations. Defensive strategies must incorporate emerging technologies while maintaining focus on fundamental human psychology principles that enable systematic manipulation.
The operational imperative is clear: building cognitive resilience requires understanding influence mechanisms, maintaining information diversity, and preserving individual agency within legitimate organizational structures.
REFERENCES
- Cialdini, R. (2006). Influence: The Psychology of Persuasion. Harper Business
- Hassan, S. (2015). Combating Cult Mind Control. Freedom of Mind Press
- Japanese National Police Agency (1995). Investigation Report: Aum Shinrikyo Chemical Weapons Program
- Stein, A. (2017). Terror, Love and Brainwashing: Attachment in Cults and Totalitarian Systems. Routledge
- U.S. Department of Justice (2018). United States v. Raniere et al. Case Documentation