SITUATION ASSESSMENT
In October 2022, researchers at Stanford Internet Observatory documented a coordinated influence operation targeting midterm elections across multiple U.S. states. The campaign employed sophisticated psychological manipulation techniques, including emotional priming through fabricated local news stories and social proof manipulation via artificial grassroots movements. What made this operation particularly concerning was not its scale, but its precision — demonstrating advanced understanding of cognitive vulnerabilities in democratic decision-making processes.
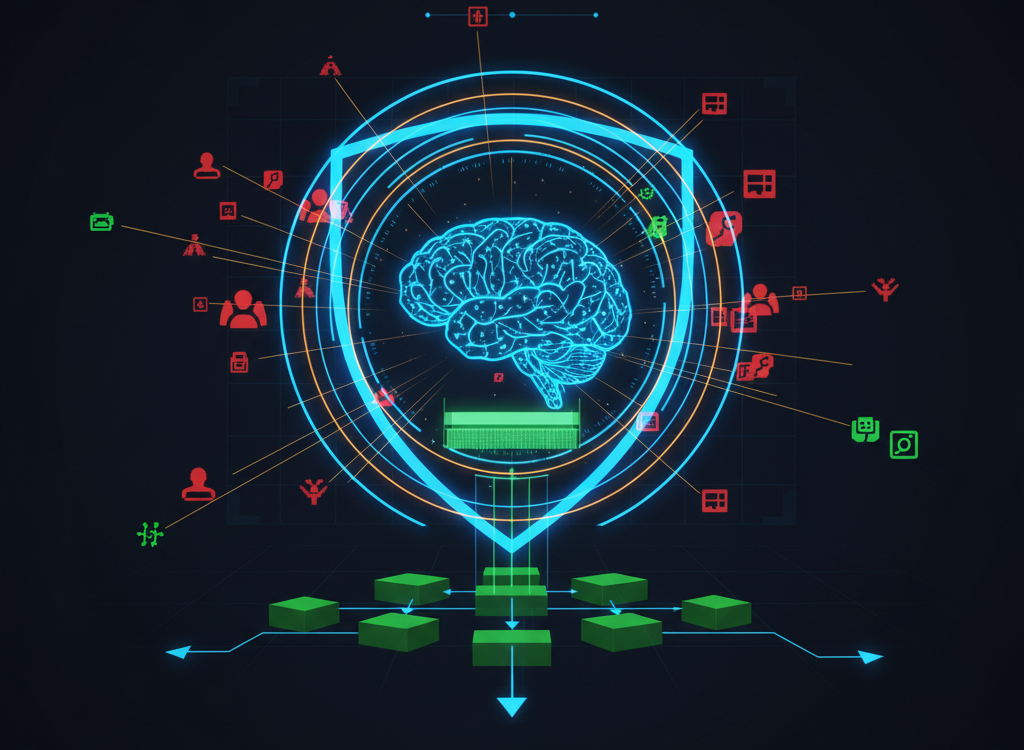
This incident represents a critical evolution in information warfare: the systematic exploitation of human cognitive processes to achieve strategic objectives. Cognitive defense emerges as the essential countermeasure to these attacks on human decision-making infrastructure.
THREAT VECTOR: Understanding Cognitive Warfare
Cognitive defense represents the systematic protection of individual and collective decision-making processes against deliberate manipulation attempts. Unlike traditional cybersecurity that protects digital systems, cognitive defense shields the human elements of information processing from hostile influence operations.
NATO’s 2021 cognitive warfare framework defines this threat domain as targeting «the human domain» — the space where perceptions, beliefs, and decision-making processes operate. Open-source evidence indicates that state and non-state actors increasingly view cognitive terrain as a primary battlespace, employing what researchers term «weaponized information» to achieve strategic objectives without kinetic force.
The RAND Corporation’s 2016 analysis identified the «Firehose of Falsehood» model as a core cognitive attack vector, characterized by high-volume, multi-channel, rapid, continuous, and repetitive messaging designed to overwhelm analytical capacity.
Cognitive attacks exploit well-documented psychological vulnerabilities. Kahneman’s dual-process theory explains how System 1 thinking — fast, automatic, and emotional — becomes the primary target for influence operations. Attackers leverage Cialdini’s influence principles, particularly social proof and authority, to bypass critical analysis and trigger desired behavioral responses.
Core Attack Mechanisms
The operational pattern suggests three primary cognitive attack vectors:
- Attention capture — overwhelming information environments to prevent deliberative processing
- Emotional hijacking — triggering fear, anger, or tribal responses that suppress rational analysis
- Reality fragmentation — creating competing narrative frameworks that undermine shared factual foundations
CASE STUDY: Documented Cognitive Operations
Operation: Brexit Influence Campaign
The UK’s Electoral Commission and subsequent academic research documented extensive cognitive manipulation during the 2016 Brexit referendum. Analysis by the Reuters Institute revealed systematic deployment of micro-targeted emotional content designed to activate specific psychological triggers within demographic segments.
Key techniques included:
- Emotional priming through fear-based messaging about immigration and sovereignty
- Social proof manipulation via artificially amplified support demonstrations
- Authority exploitation through fabricated expert endorsements
The operation demonstrated sophisticated understanding of cognitive biases, particularly confirmation bias and availability heuristic, to reinforce pre-existing beliefs while making extreme positions appear mainstream.
Operation: COVID-19 «Infodemic»
WHO and EU DisinfoLab documented coordinated cognitive attacks during the COVID-19 pandemic, with threat actors exploiting health anxiety to promote political objectives. The operational framework targeted trust in institutions through systematic undermining of scientific authority.
This aligns with documented TTPs (tactics, techniques, and procedures) for cognitive warfare: exploiting crisis conditions when analytical capacity is reduced due to stress and uncertainty. DFRLab analysis identified coordinated networks spreading contradictory health information designed to create decision paralysis rather than promote specific beliefs.
DETECTION PROTOCOL: Cognitive Attack Indicators
A critical indicator analysis reveals consistent patterns across cognitive operations. Intelligence suggests the following behavioral signatures indicate active cognitive targeting:
Technical Markers
- Coordinated amplification — identical messaging across multiple platforms with timing synchronization
- Emotional intensity metrics — content specifically designed to trigger strong emotional responses rather than inform
- Source obscuration — deliberate hiding of funding sources, authorship, or organizational backing
- Micro-targeting evidence — highly specific demographic targeting suggesting psychological profiling
Content Patterns
- Emotional escalation — progressive increase in emotional intensity over time
- False urgency — artificial time pressure to prevent deliberative analysis
- Simplistic solutions — complex problems presented with unrealistically simple answers
- Tribal signaling — excessive in-group/out-group language designed to activate tribal psychology
Behavioral Indicators
- Rapid belief changes without corresponding evidence exposure
- Increased certainty about complex issues following information consumption
- Reduced tolerance for uncertainty or nuanced positions
- Automatic sharing behavior without content evaluation
DEFENSE FRAMEWORK: Multi-Layer Cognitive Protection
Assessment: Effective cognitive defense requires coordinated implementation across individual, organizational, and systemic levels. Evidence-based countermeasures include:
Individual Cognitive Hygiene
- Source verification protocols — systematic checking of information origins before belief formation or sharing
- Emotional regulation techniques — recognizing emotional manipulation attempts and implementing pause protocols
- Diverse information diets — deliberately seeking multiple perspectives on important issues
- Metacognitive awareness — understanding personal cognitive biases and vulnerability patterns
Organizational Defense Measures
- Decision-making protocols — implementing structured analysis techniques that resist cognitive attacks
- Information verification systems — institutional processes for fact-checking and source validation
- Cognitive security training — regular education on influence operation tactics and defensive techniques
- Diverse team composition — leveraging cognitive diversity to resist groupthink and manipulation
Systemic Countermeasures
Policy-level cognitive defense requires coordinated efforts across multiple domains:
- Platform accountability — requiring social media companies to implement cognitive defense features
- Media literacy education — systematic integration into educational curricula
- International cooperation — sharing threat intelligence and defensive techniques across allied nations
- Research investment — funding cognitive security research and development
Recent research by the Atlantic Council’s Digital Forensics Lab demonstrates that societies with robust media literacy programs show significantly higher resistance to influence operations, with effect sizes comparable to traditional cybersecurity investments.
ASSESSMENT: Key Intelligence Takeaways
Critical findings from this analysis:
- Cognitive warfare represents an active and evolving threat — documented operations show increasing sophistication in psychological targeting techniques
- Individual awareness alone insufficient — effective defense requires coordinated individual, organizational, and systemic countermeasures
- Detection capabilities improving — open-source research organizations developing reliable indicators for cognitive attack identification
- Defensive technologies emerging — AI-assisted fact-checking and cognitive security tools showing promise in controlled studies
- International coordination essential — cognitive threats cross borders and require multilateral defensive cooperation
Forward Assessment
The cognitive defense landscape will likely see increased integration with traditional cybersecurity frameworks as organizations recognize human decision-making as critical infrastructure requiring protection. Early indicators suggest that nations investing in cognitive resilience now will maintain strategic advantages as information warfare continues evolving.
What is cognitive defense ultimately represents humanity’s adaptation to weaponized information environments — developing systematic approaches to protect the integrity of human judgment in an era of sophisticated psychological manipulation.